Because of technical limitations, Drive Badger project is divided into 2 separate products, sharing the same source code, the same configuration and extensions, but run in a different way:
Drive Badger
Is installed on your USB drive, and it uses Kali Linux, which is the Linux distribution focused around security (pentesting etc.). It runs directly on the victim computer, detects your external drive as well as all other drives, and exfiltrates data to your USB drive.

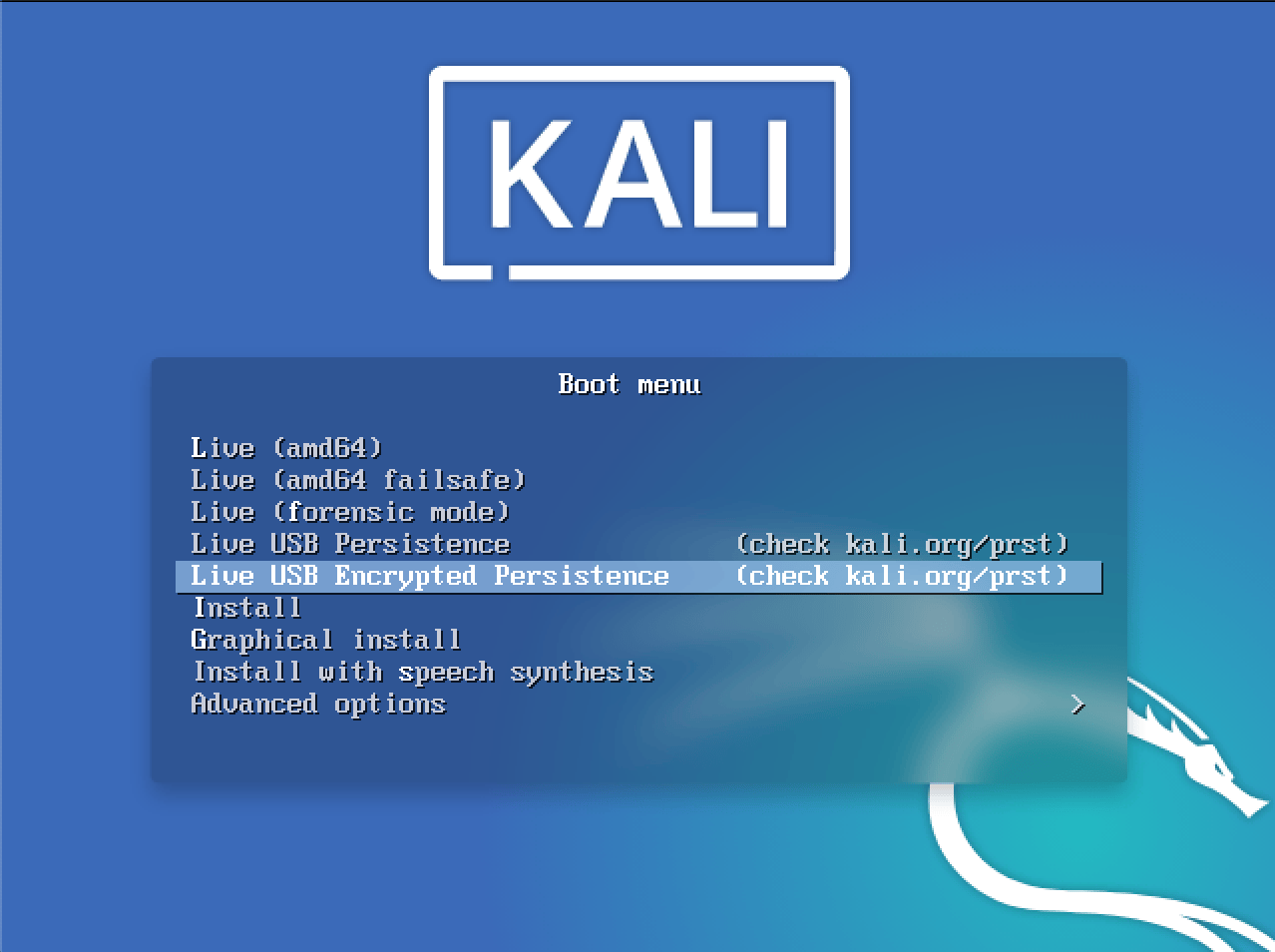
For operator safety, Drive Badger boots only after manual choosing "Live USB Persistence" or "Live USB Encrypted Persistence" option in Kali Linux boot menu. In case of no action, ordinary Kali Linux is run, without access to the partition containing exfiltrated data, and Drive Badger code itself.
Mobile Badger
Is installed on your own computer (Raspberry Pi, laptop, or even desktop computer), and it uses Debian, Ubuntu, Raspbian or Kali Linux. Computer with Mobile Badger recognizes connected:

-
Mobile devices (all brands and models that connect to the computer using USB, and support either MTP or PTP protocol for transferring data):
- Android phones, tablets and possibly other devices
- iOS-based devices (iPhone, iPad)
- Windows Phone 8/10 (Lumia phones)
- Symbian
-
USB Mass Storage devices:
- mobile devices not supporting MTP/PTP (eg. some older phones)
- mobile devices configured as mass storage (phones, mp3 players, photo cameras etc.)
- pen drives
- external USB drives
- internal drives connected via USB bridge (eg. pulled from computers, where standard Drive Badger cannot be run, because all USB ports are damaged)
- including drives encrypted using Bitlocker, LUKS, VeraCrypt or APFS with Apple FileVault, using the same exclusion rules and key configuration methods, that are used by Drive Badger
All recognized devices (except for ignored ones) are automatically exfiltrated: either to target USB drive, or internal memory card ("fallback storage" mode).
Mobile Badger, as opposed do Drive Badger, doesn't need any screen or keyboard to run. It runs fully headless, and all events are shown on external LCD/LED display device.