If you're looking for recommended external storage devices, go to this page instead.
Mobile Badger can be run on any hardware, that:
- has at least 2 working USB ports (in some circumstances, just 1)
- is able to run Debian, Ubuntu, Kali Linux, Raspbian (or any other Debian clone) with systemd version 229 or newer (released 2016+)
This includes Raspberry Pi and its clones (if you expect discretion and mobility above all), through laptops, desktop computers, to servers. On this page you will find our insights and recommendations about choosing the proper hardware for your particular needs.
Key factors for choosing the best hardware
There are 8 key factors, that you should consider:
- your modus operandi (it determines all the rest, and it may differ between attacks):
- mobile, covert/concealed use
- mobile, explicit use
- stationary
- power (consumption, stability on not enough power, cooperation with power banks)
- general CPU and I/O performance
- number of available USB 3.0 (or newer) ports
- compatibility with display devices
- emphasis on standardization and interchangeability - or performance maximization (mobile version)
- working temperature and cooling issues (mobile version)
- encryption support (available on laptops only)
Mobile device for concealed use - what to choose and why?
If you plan to work fully concealed (and also mobile), laptop - even small and lightweight - won't be an optimal choice. What you're looking for is Raspberry Pi platform - both original and its various clones.
- by choosing original Raspberry Pi, you gain easy replaceability (these devices are wide known and used, easy to buy and replace, and subsequent versions are backwards compatible)
- by choosing clones (and there are lots of them) you can gain some particular advantages: smaller size, better performance, integrated GSM modem etc. - but also you you risk its inaccessibility in stores in the future, mixed with compatibility problems (which means that your application might need changes, or even redesign in the future)
As for Mobile Badger and concealed use, Raspberry Pi 4 won't be a good choice, since it suffers 2 problems:
- overheating, especially during heavy load (passive cooling is not enough, standard 30mm fan is noisy and still enough only in cooled rooms)
- excessive power usage (requires 3A)
If you want to choose an original Raspberry Pi, choose 3B model, which is quite slow, but it doesn't have any temperature-related issues, and can work fully hidden. However, our choice is NanoPi platform (see below).
How many USB ports and why?
Above we stated that you need at least 2 working USB ports. In fact, the exact number of required USB ports depends on planned usage. USB ports - apart from power port in Raspberry Pi - are required for 3 things:
- Connecting exfiltrated drive or other device:
- USB 3.0 or later is preferred
- depends on CPU performance, you may need more than 1 such port (to exfiltrate a few drives at once)
- Connecting target drive:
- USB 3.0 or later is preferred
- for fully concealed use, exfiltration directly to internal memory card (fallback storage mode) may be a better choice - you don't need a sepate USB port then
- Connecting external USB display device, eg. BlinkStick Strip - for Raspberry Pi and its clones you will rather use GPIO-based devices, and you won't need this port - but in some case you'll want to use external display instead. USB 2.0 port is enough for this.
Exfiltration to internal memory card - when does it make sense?
Both Raspberry Pi platform and its clones (including NanoPi) use MicroSD memory cards to store the main filesystem. Mobile Badger can save exfiltrated data either to external target drive, or internal memory card (this mode is called "fallback storage").
Functionally, using internal memory card is better in 3 cases:
- in fully concealed use, when you need to minimize and hide all your equipment, however you have a lot of time and the exfiltration process can take much longer
- when you need to minimize the power usage (eg. you have a very weak power bank or power supply)
- as spare storage, in case you have no more space on target drives, or target drives failed, were lost etc.
The biggest problem with memory cards is their low write performance, combined with relatively low durability. So you should consider all 3 above cases as emergency situations only: you definitely should be prepared, but in normal circumstances you should use external SSD drive(s).
On the other hand, in full stationary or laptop mode, when you boot your computer from SSD drive (not a memory card), then fallback storage mode is absolutely safe to use. Just remember that you need to reserve around 3-4 GB for all system data, caches, logs etc.
Recommended models
Below you'll find our 4 recommended computer models (depending on your modus operandi).
For fully concealed use: NanoPi-NEO2 + BakeBit NanoHat OLED
- absolutely the smallest one (just 40 x 40 mm)
- slow data transfers - general performance similar to Raspberry Pi 3B
- only 2x USB 2.0 ports
- only 512 MB RAM, which limits any possible future functionalities, eg. image recognition
- small power requirements, works very well with majority of power banks, cheap power supplies etc.
- uses customized version of Ubuntu 16.04 LTS
- 8-line text OLED display, showing current activities
- mini-jack sound output, 3 programmable keys, elegant case - easy to disguise as mp3 player
- price below $75
Good choice, if:
- you have plenty of time (eg. you're working with the victim 8h each day)
- you want to bring (and use) it hidden inside a protected area, without being noticed by anyone

For partially covert use: NanoPi-NEO3
- still one of the smallest models (just 48 x 48 mm)
- only 1x USB 3.0 port (requires either USB hub and BlinkStick Strip display, or working in full headless / fallback storage modes)
- faster CPU than NEO2, 2 GB RAM - enough for data exfiltration and possible future functionalities, eg. image recognition
- small power requirements, works very well with majority of power banks, cheap power supplies etc., no overheating problems
- uses customized version of Ubuntu 20.04 LTS
- comparing to NEO2: no LCD display, no buttons, no mini-jack sound output, plastic case instead of aluminum (but still good quality)
- price below $100
Good choice, if you can't entirely hide your activities, and instead want to disguise them to prevent raising questions - eg. use one of BlinkStick display device, built into some bigger construction, like police car dashboard.

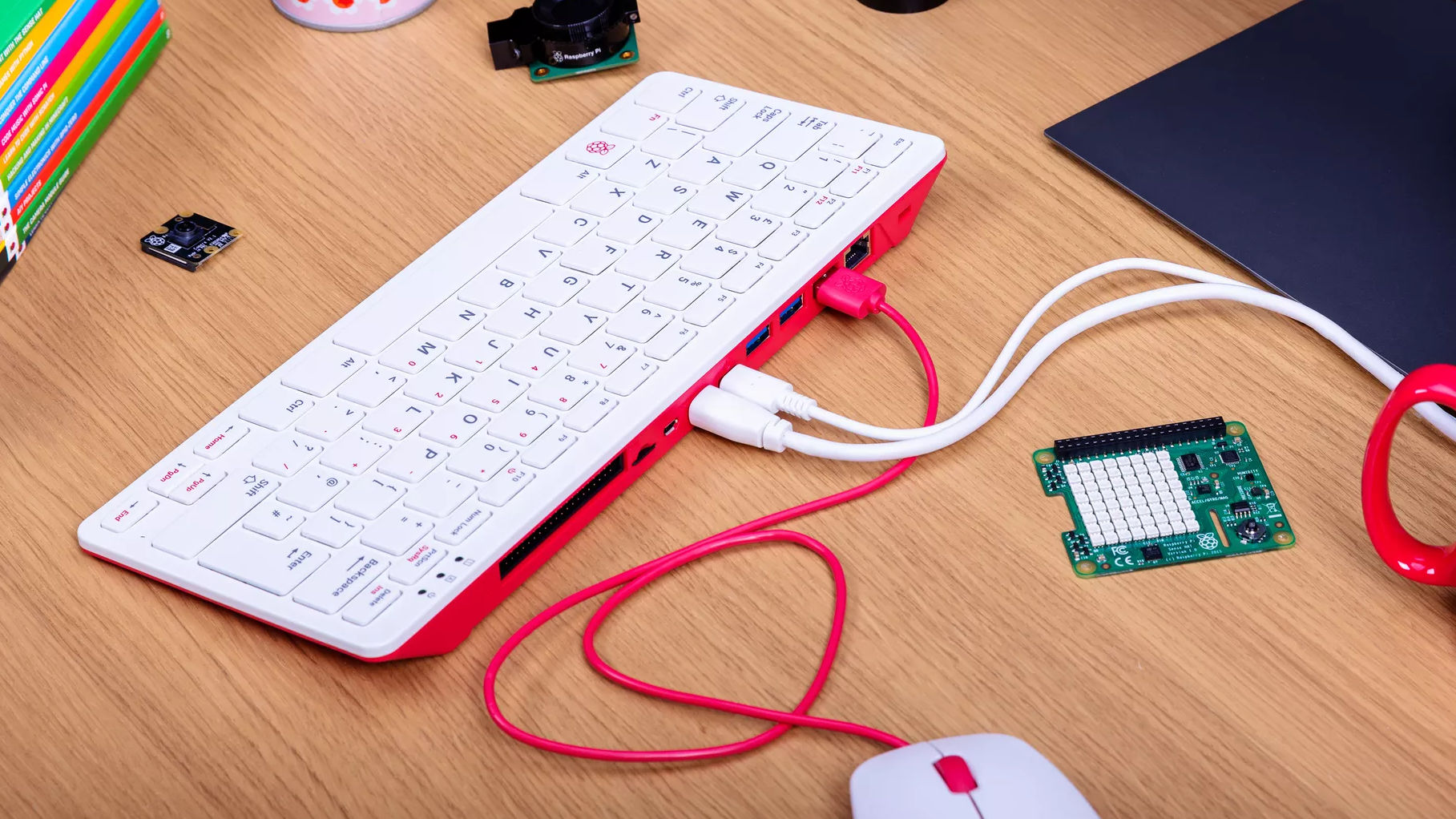
For mobile, but explicit use: Raspberry Pi 400
- the fastest version of Raspberry Pi, with resolved overheating problem from Raspberry Pi 4
- 6-7x better CPU performance than Raspberry Pi 3B or above NanoPi-NEO2
- 2x USB 3.0 ports + 1x USB 2.0
- very power-hungry, requires USB power supply with real 3A or more (such power supplies or power banks are quite massive, which can be problematic in the field - choosing an ordinary laptop can be a better option then)
- tested with Anker PowerCore Select 20000 mAh power bank with 3A output (390g weight), works over 20h on idle
- 2x HDMI output (for 2 monitors) - assuming that there will be no problem with external HDMI monitors in the attacked place, it's still smaller, lighter and way less expensive than dedicated laptop
- compatible with most Raspberry Pi extensions, including Pimoroni Blinkt (Mobile Badger can display current activities using customizable color codes on Blinkt - so monitor is not required)
- uses either Raspbian Buster or Ubuntu 20.04 LTS for ARM (both 32 and 64 bit versions)
- price below $100
Good choice, if you don't need to hide your equipment, but still need it to be mobile.
For stationary use: Dell Optiplex 7040 Micro
- this particular model has 6x USB 3.0 ports, external power supply and case small enough to treat it as a mobile device
- Intel Core i5-6500T CPU gives totally outstanding performance, comparing to the above models
- you can install Debian Stretch/Buster, Ubuntu 18.04 / 20.04 LTS, or their any derivative (Mint, Mate, Kubuntu etc.)
- price below $300 (used, in very good condition, without SSD)
Good choice, if you exfiltrate data from mobile devices at your place (instead of in-the-field), especially if you do it at bigger scale (court laboratory etc.).