On HP desktop/laptop with TPM 2.0, pre-installed Windows 10 boots without any passwords, but Drive Badger sees the drive as Bitlocker-encrypted
New HP computers (at least since 2019), that are sold with pre-installed Windows 10, come with pre-enabled Bitlocker drive encryption in passwordless mode (the only authentication key is stored in TPM 2.0 module). So the computer boots without asking user for password, but when booted from external drive, Windows partition is encrypted.
The solution is to obtain Bitlocker recovery key, and add it to Drive Badger Bitlocker keys configuration:
-
Windows 10 Pro - there are many methods to do this, just follow the instructions.
-
Windows 10 Home uses a simplified, restricted and unbranded version of Bitlocker, with only one method to recover the key: synchronize it with Microsoft account. When done properly, you will find the key at this address. However this requires first login to a Microsoft account - if you skip Wi-fi connection step and force creating a local account, it is no longer possible to synchronize the recovery key, and it can't be fixed without decrypting and encrypting again the drive (see below).
Required conditions, when the problem occurs
- HP hardware with TPM 2.0 with Modern Standby support - eg. HP 14s series of cheap laptops with AMD Ryzen
- pre-installed Windows 10 Home
- pre-enabled drive encryption (simplified Bitlocker) in passwordless mode (boots without asking for any passwords etc.)
- on first login, Wi-fi skipped and Windows initialized with and offline account
- additional conditions may be needed
In such conditions, drive encryption is still enabled and requires data from TPM to boot. TPM failure or resetting its data from Windows TPM console, effectively destroys the Windows partition.
After logging in for the first time to offline (non-Microsoft) account:
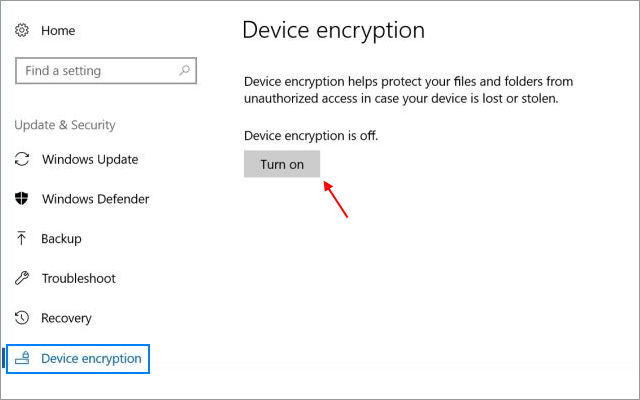
- drive is still encrypted, but encryption is marked as "suspended"
- it is no longer possible to synchronize the recovery password with any Microsoft account
- there are no other option to get the recovery password, or change the user password (print and local save options are disabled)
Solution 1:
- decrypt the drive, by clicking "Turn off" at the above dialog (it will show a red error message, that device encryption is suspended)
- convert your local account to a new/existing Microsoft account (probably logging on to existing Microsoft account would help, but we didn't test it)
- reboot
- uninstall any McAfee software (probably it would be enough to relax the protection level for a while, but again we didn't test it)
- reboot
- go to Control Panel System menu and change both computer hostname and workgroup name (using classic dialog - note there is also a Windows 10 dialog to change the hostname only, without the option to change domain/workgroup - don't use it, instead seek for "advanced" hostname change dialog)
- reboot and wait - Windows should start encrypting the drive
- check this address for recovery key - it will probably be synchronized under the old hostname
After each reboot, keep the computer working for at least 5 minutes. In fact, drive encryption wasn't "factory-enabled", but is enforced by HP settings - so when you unblock the possible problems, it will turn on again automatically.
Solution 2 (untested):
Try to use Surface BitLocker Protector Check tool from Microsoft. It can help with various problems with Bitlocker on Microsoft Surface Book devices - and possibly others, based on your TPM 2.0 provider.
Solution 3 (untested):
Try to upgrade from Windows Home to Windows Pro, using Windows Store. This should unlock other methods of revealing recovery key, as well as unlock all Bitlocker features and settings.